 The topic of cybersecurity is more pertinent than ever, as cyberattacks pose one of the most significant threats to businesses. Unfortunately, the pivotal role of cybersecurity is often overlooked, due to a prevailing misconception that cyberattacks primarily target major retailers or large corporations. In actuality, cyberattacks can happen to any business, of any size.
The topic of cybersecurity is more pertinent than ever, as cyberattacks pose one of the most significant threats to businesses. Unfortunately, the pivotal role of cybersecurity is often overlooked, due to a prevailing misconception that cyberattacks primarily target major retailers or large corporations. In actuality, cyberattacks can happen to any business, of any size.
Companies must take immediate action to address the mounting threat to their security posed by the growing scale and frequency of cyberattacks.
This blog will explore the importance of cybersecurity, common cyberthreats, and proactive measures businesses can take to protect themselves.
The Basics & Importance of Cybersecurity
CISA defines cybersecurity as the art of protecting networks, devices, and data from unauthorized access or criminal use. The rise in technology has led to an increase in cyberthreats, and cybersecurity is critical to ensuring defense.
Most cyberattacks aim to obtain and exploit sensitive data for personal or financial gain. This can include stealing, exposing, altering, or destroying data.
A security breach can expose sensitive information such as credit card details, social security numbers, login credentials, and bank account information, which can result in identity theft, financial loss, or business disruption.
Common Cyberthreats
Businesses rely heavily on technology and data to operate efficiently; however, this reliance also makes them susceptible to a wide array of threats. Cyberattacks on businesses have become increasingly common and sophisticated, posing significant risks to data, finances, and reputation.
While any business can fall victim to a cyberattack, small businesses are particularly vulnerable, as they often lack the resources and budgets larger firms have access to.
The most common cyberthreats businesses face:
-
Phishing: The cybercriminal poses as a reliable entity to trick users into divulging sensitive information or personal data. This is one of the most common forms of attack and is typically carried out through emails, texts, phone calls, and other forms of communication.
-
Malware Infection: Malware, or malicious software, is designed to steal data and damage computer systems. Ransomware is a
 common malware attack.
common malware attack. -
Ransomware: Ransomware is a type of malware attack that encrypts the victim’s data or device, threatens to keep it locked, and then demands payment in exchange for access, essentially holding their data ransom. Ransomware is one of the most financially damaging cyberattacks.
- Distributed Denial of Service (DDoS): A DDoS is an attack that overwhelms a website, network, or system with volumes of fraudulent traffic, making it too slow for legitimate users. The cybercriminals attempt to crash the targeted system in order to gain control.
-
Supply Chain Attacks: The cybercriminal uses the vulnerability of an outside supplier’s security system to gain access to the targeted organization’s network.
-
Man-in-the-Middle (MinM): The cybercriminal positions themself between two communicating parties to intercept their data. The attack is a type of eavesdropping in which the attacker seizes and then controls the conversation between the parties.
-
Internet of Things (IoT) Attack: Cybercriminals exploit vulnerabilities in IoT devices to take over the devices, steal data, or use the devices as part of other malicious attacks.
-
Insider Threat: Threats that originate with authorized users who intentionally or unintentionally misuse their access, have their accounts hijacked by cybercriminals, or compromise the security of the organization’s computer systems, data, or networks.
Prevention Strategies
Cyberattacks can have significant and far-reaching consequences – both immediate and long-term. They often affect companies' revenue, respectability, and operational capabilities.
According to Accenture’s Cost of Cybercrime Study, 43% of cyberattacks are aimed at small businesses, but only 14% are prepared to defend themselves.
The best way to proactively prevent cyberattacks is to employ robust prevention strategies. Here are some measures you can take to protect your business: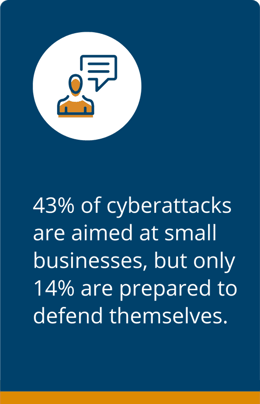
-
Use strong passwords and change them often.
-
Keep software and applications up to date to avoid vulnerabilities.
-
Be wary of suspicious emails and avoid clicking on links from unknown senders.
-
Use reputable anti-virus and anti-malware software and install firewalls for all devices and networks.
-
Implement multi-factor authentication for sensitive data and apply encryption measures to protect it.
-
Limit employee access to data and their authority to install software.
-
Create a well-defined response plan to minimize the impact of an attack.
- The Federal Trade Commission has created a data breach response plan for businesses to reference in the unfortunate event of a cyberattack.
In addition to adopting these strategies, educating employees on the dangers of cyberattacks can help your business avoid their severe repercussions.
Protect Your Business
Cybersecurity is a critical aspect of modern-day business operations. Every company is a target, and operations, reputation, and revenue are at stake. But taking certain precautions can help mitigate your cybersecurity risk.
By prioritizing cybersecurity, adopting cyberattack prevention strategies, and understanding how to respond effectively to attacks, you can navigate the evolving digital landscape with confidence.
Flagship understands the constant danger cyberattacks pose to businesses and their severe repercussions. Implementing the right IT solutions is paramount to your security.
We offer IT services that can protect your business and your bottom line. From data backup and recovery to cybersecurity, our expert technicians deliver exceptional solutions tailored to your needs.
For more information about our IT solutions, visit our tech services page.





Leave a Comment